Azure AD Ignite Recap 3: start your journey to password-less!
| Hey there folks! It's been a great (and busy) few months couple of months since the last update. For this third recap, we're going to focus on something really critical to our long term security strategy. Every day, the Identity Security and Protection (for which I serve as Group Program Manager) intercepts around 400M criminal login attempts. Do the math, and we're talking something like 12 billion fraudulent requests a month! Virtually all of these are opportunistic attacks which rely on password re-use, guessable passwords, and password phishing. What's the common denominator?
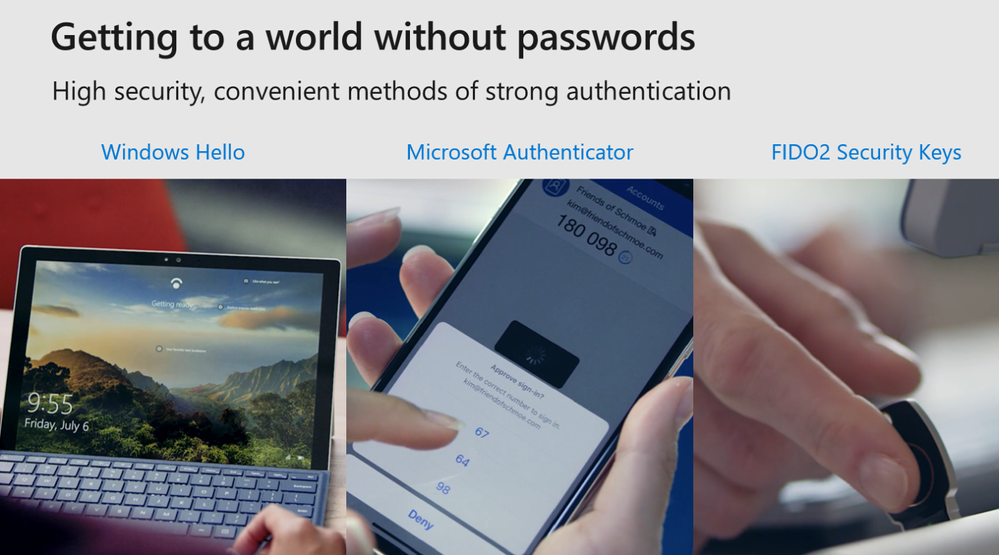
I use multi-factor authentication in each of the many work and personal systems where I have an account. Typically this means entering a password in conjunction with a code generated by my Microsoft Authenticator App, but for my Microsoft account and Azure AD accounts, I can sign in with the app directly. This is both much easier and more fun and more secure than old-style multi-factor authentication. Lately I have been having a blast showing off FIDO2 logins to my Microsoft accounts (you can learn a ton about the protocols in this blog post from Pam Dingle (@pamelarosiedee).
Stay safe! -Alex (@alex_t_weinert) ---
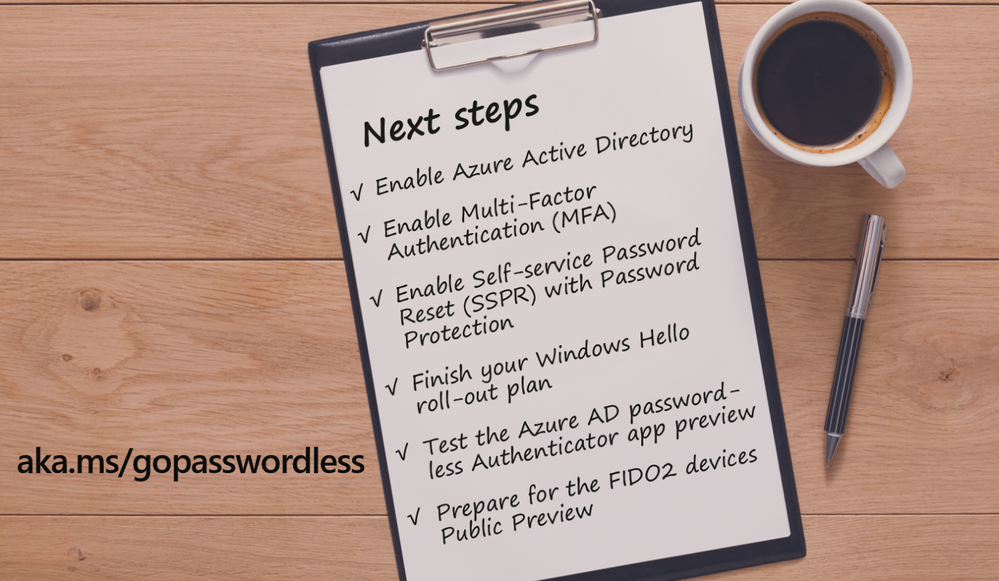
Download the whitepaper now: Microsoft Password-less Protection Since our announcements at Ignite, we want to share some key updates around our password-less solutions: Authenticator app We've seen great interest in the public preview of signing in password-lessly with Microsoft Authenticator! Since Ignite, over 1,200 tenants have acted to enable the policy and begin using it, and our weekly active usage has more than tripled. If you are interested in trying it out for your tenant, please be sure to read Password-less phone sign-in with the Microsoft Authenticator app for instructions and known issues. We also heard your requests to have a more granular level of control for the use of this credential. In the first half of 2019, we will be adding a powerful tool-the ability to assign use of this credential, and others, to users and groups-to help you with your pilot and rollout projects. Fast Identity Online (FIDO) Alliance On November 20, 2018, we started rolling out the ability for our Microsoft account users to sign in to Microsoft Edge using a FIDO2 device or Windows Hello. This will allow about 800 million users to access their Microsoft services on the web without a password (or even a username). Under the covers, we've implemented the WebAuthn and CTAP2 specifications from the FIDO2 standard into our services to make this a reality. As a member of the FIDO Alliance, we have been working with other alliance members to develop open standards for the next generation of authentication. We are happy that Microsoft is the first company to support password-less authentication with FIDO2. For more information and to try it out, read this blog post.
Overall, we are making great progress and you can start your password-less journey today. We have enabled our password-less solutions to work in cloud scenarios, so as you are making your move to Azure Active Directory (Azure AD), it's a great opportunity to envision what the future of authentication will look like without breaking any of your existing scenarios. It's also important to pilot and deploy the solutions that are available in order to get your employees to stop relying on passwords for their everyday authentication. It'll make their lives easier day-to-day and they'll be more suspicious when asked for their username and password by phishing scams and malware. In the meantime, as you are piloting these solutions, you can tell us what you think so your feedback can feed into the product design cycle. It's a win-win for all of us! Get started on your password-less journey Excited? Start by reading the Microsoft Password-less protection document and then start piloting one of the Microsoft password-less solutions.
|
Comments
Post a Comment